7. Firewall zones and rules
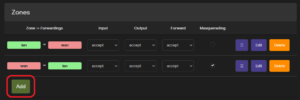
Zones
The firewall can group interfaces into zones for which rules, forwards, and redirects can be set, allowing for more logical traffic filtering. Any interface can be grouped into zones, but generally, there are zones collecting LAN and WAN interfaces.
Configuring zones
Zones can be configured in the router interface section Network -> Firewall -> General Settings.
The Zones section shows current zones and forwarding rules, and a new zone can be added using the Add button.
When creating or editing a zone, default properties, such as Input, Output, and Forward, can be set:
- Input: Policy for incoming traffic.
- Output: Policy for outgoing traffic.
- Forward: Set policy for traffic between the networks within the zone.
Which networks are assigned to the zone can be set under Covered networks.
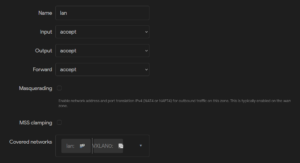
Forwarding between zones is set by selecting the zone to which traffic can be forwarded from the current zone in Allow forward to destination zones, and selecting the zone from which forwarded traffic is accepted in Allow forward from source zones. The forwarding rule is unidirectional; e.g., a forward from lan to wan does not imply permission to forward from wan to lan as well.

Adding interfaces to zones
Individual interfaces (Network -> Interfaces -> Interfaces) can be assigned to a zone when creating or editing an interface under the tab Firewall Settings.

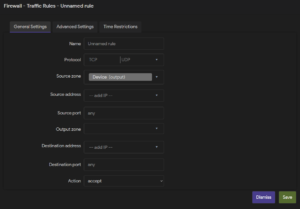
Firewall – Traffic Rules
Firewall (traffic) rules are used to control traffic flow in a firewall. They allow us to specify packets based on criteria such as protocol, zones, IP addresses, and ports and apply actions (accept, reject, drop, etc). Firewall rules control how the firewalls prevent malicious programs and unauthorized traffic from compromising your network.
Traffic rules configuration
The firewall rules can be set in the interface under Network -> Firewall -> Traffic Rules

New rules can be added by using the Add button at the bottom of the page. When creating new rules it is recommended to use a naming scheme, for easier maintenance and debugging. New rules can filter packets by:
- Protocol
- Source
- Zone
- IP address
- Port
- Destination
- Zone
- IP address
- Port
In the “Action” field we set the action which is applied to the filtered packets. These actions can be:
- Accept
- Reject
- Drop
- Don’t track
- Assign conntrack helper
- Apply firewall mark
- XOR firewall mark
- DSCP classification